Infrastructure as a Service (IaaS) has become a must-have asset for businesses of all sizes. It is being used in IT environments to build and host internal and customer applications. However, in the rush of adopting IaaS, the businesses are not paying enough attention to security.
According to a new report by McAfee, 99% of the misconfigurations in IaaS remain unnoticed. This shows that the businesses aren’t aware of the new Cloud-Native Breaches (CNB). They are expecting only the cloud provider to handle the security. However, IaaS is a cloud shared-responsibility model. Not having security practices in place can put the cloud and sensitive data at risk.
IaaS security: Key findings of McAfee IaaS Adoption and Risk Report
McAfee’s IaaS Adoption and Risk Report covers the IaaS security incidents in the cloud. Here are highlights of the report:
-
Rise of Cloud-Native Breaches
IaaS environments experience several security incidents, but these incidents are different from the typical malware-based attacks. Mostly, there are Cloud-Native Breaches (CNBs), which capitalizes on the misconfigured, native features of the cloud.
McAfee defines CNB as an opportunistic attack on the data left open by errors in the way cloud environments are configured.
Also read: Organizations have 14 misconfigured public cloud services running at any given time: McAfee study
-
Only 1% of misconfigured IaaS incidents are known
Businesses are aware of only 1% of IaaS security incidents. Respondents said that they witness average 37 such incidents every month. However, the reality is they experience 3,500 incidents per month.
This shows that 99% of misconfigurations are remaining unnoticed by companies.

-
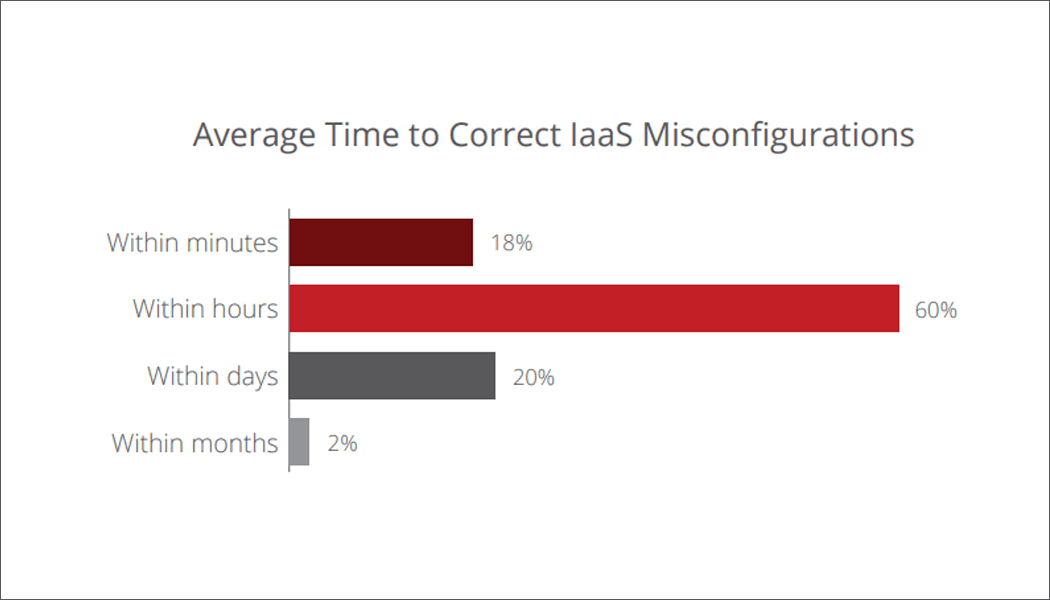
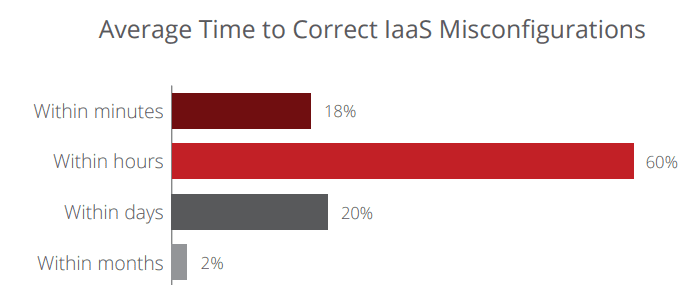
Enterprises taking plenty of time to correct IaaS misconfigurations
When asked about the time taken to fix the IaaS misconfigurations, around a quarter of businesses take more than a day to fix it. This means that the attackers have a lot of time to scan for open ports and carry out the attack.
Only 18% of businesses correct the misconfigurations within minutes.
-
Only 26% of companies able to audit IaaS misconfigurations
McAfee finds that only 26% of businesses are able to audit the IaaS misconfigurations using existing security tools.
The reason behind most of the businesses not having the right tools in place is that there is a disconnect between CXOs and IT practitioners. 90% of businesses reported some sort of IaaS security issues. However, most of the IT managers believed that they never experienced such issues.

Related reading: Legacy tools put organizations to survival mode rather than digital transformation: Forrester
-
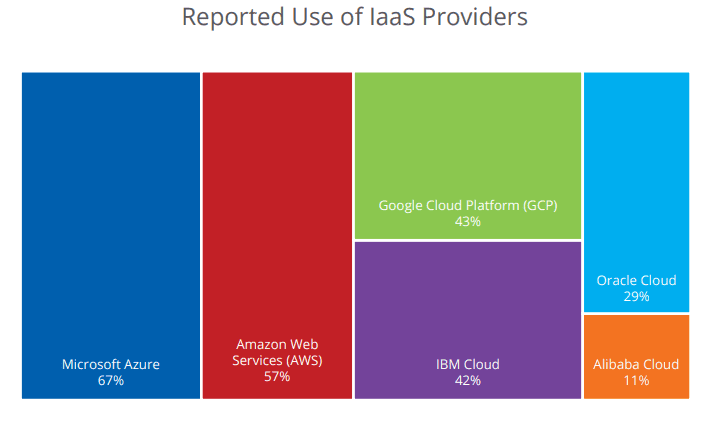
92% of businesses use multiple IaaS providers
When asked about the number of IaaS service providers being used, 76% of respondents said that the multiple IaaS providers. However, the real-world data by McAfee shows that 92% of businesses are actually using multiple providers.
This reveals that security incidents are going to occur if the businesses aren’t even aware of where their infrastructure lives.

-
Azure and AWS—most used IaaS providers
Microsoft Azure (67%) and Amazon Web Services (AWS) (57%) are used by most of the businesses for IaaS services. Google Cloud Platform (GCP) and IBM Cloud are used almost equally, followed by Oracle Cloud and Alibaba Cloud.
Suggested reading: 48 million social media records exposed publicly in misconfigured cloud instance
Best practices to mitigate IaaS security incidents:
The leading IaaS providers including AWS, Microsoft, Google, and others are continuously upgrading and making things easier for businesses to deploy infrastructure. But to reduce the overall risks, the businesses will need to follow some best practices, as follows:
- Develop IaaS configuration auditing into the CI/CD processes
- Evaluate the IaaS security practices using a framework
- Invest in cloud-native security tools
- Train the security teams
For detailed insights, download the full Cloud-Native: The Infrastructure-as-a-Service (IaaS) Adoption and Risk Report.
Images source: McAfee