Cybersecurity has become an increasingly important concern for businesses and individuals alike in recent years. With the rise of remote work and cloud computing, the traditional security perimeters that once kept sensitive data safe are no longer effective. In response, many organizations are turning to zero-trust security to protect their networks and assets.
Okta’s research shows that the proportion of companies that have already started a defined Zero Trust initiative has more than doubled, from 24% in 2021 to 55% in 2022. In 2019, just 16% of organizations had put in place or planned to implement Zero Trust security, a figure that has since surged to 97% in 2022.
But what exactly is zero trust security, and why does it matter to you?
In this article, we’ll explore the basics of zero trust security and its potential benefits for both individuals and organizations. Whether you’re a cybersecurity professional or simply interested in keeping your data safe, understanding zero trust security is an essential step in today’s digital landscape.
What is zero trust security?
Traditionally, businesses have relied on a “castle-and-moat” approach to cybersecurity, whereby anyone outside of the corporate network is deemed suspicious while those inside are considered trustworthy. This implicit trust in internal users has led to numerous expensive data breaches, as attackers who breach the perimeter can move horizontally through the network.
The zero trust model differs in that it continuously authorizes and authenticates throughout the network, rather than just at the perimeter. This approach limits unnecessary lateral movement between apps, services, and systems, taking into account both insider threats and the possibility of attackers compromising legitimate accounts. By restricting access to sensitive data, the number of opportunities for hackers to steal it is significantly reduced.
Zero Trust represents a framework designed to secure infrastructure and data amid the modern digital landscape. It presents a unique solution to address the challenges of remote workers, hybrid cloud environments, and ransomware threats that businesses face today.
The Zero Trust security framework mandates that all users, both within and outside the organization’s network, must be authenticated, authorized, and consistently validated for security configuration and posture to gain or retain access to applications and data. Unlike traditional security models, Zero Trust assumes the absence of a network edge, with networks potentially being local, cloud-based, or a hybrid of both, with resources scattered anywhere and employees operating from any location.
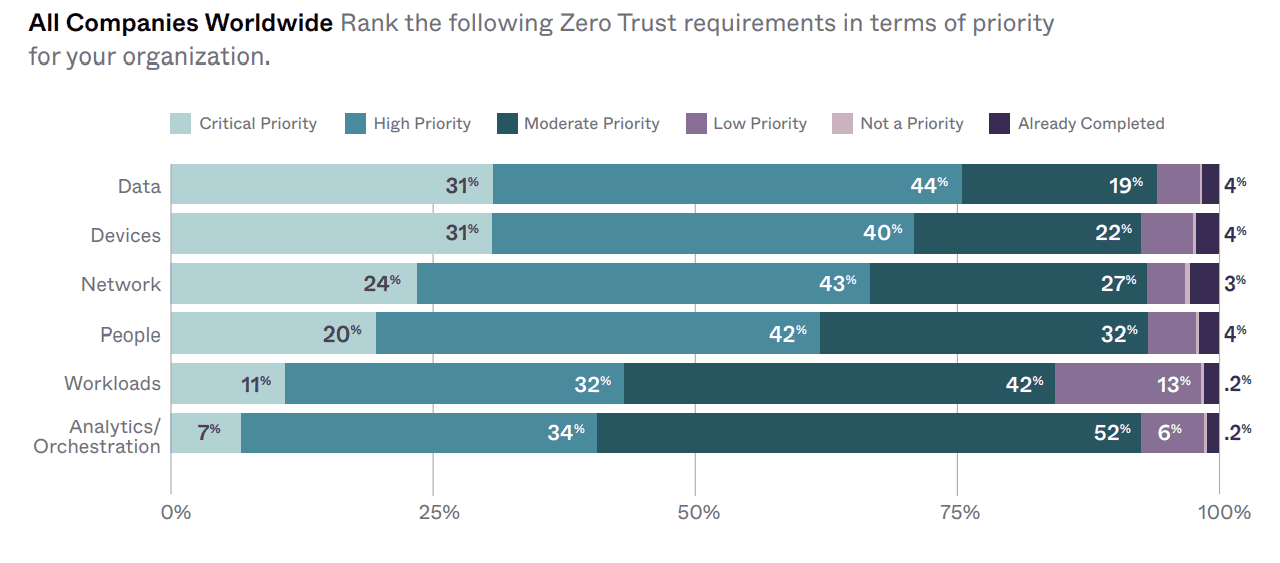
Image source: Okta
Why should organizations implement a zero trust model?
To remain competitive, security teams must implement a Zero Trust network architecture to safeguard enterprise data, regardless of user and device location, while ensuring seamless and swift application performance.
The Zero Trust architecture offers several benefits, including seamless user experience, minimized attack surface, improved cybersecurity, and simplified infrastructure requirements. The various components of Zero Trust architecture enable the following:
Increased security: With a zero trust model, all network traffic, devices, and users are treated as untrusted. This means that every access request is thoroughly scrutinized and verified before granting access. This approach helps reduce the risk of data breaches and cyber-attacks.
Protection against insider threats: One of the significant benefits of a zero trust model is that it can help mitigate the risk of insider threats. In traditional security models, once a user gains access to the network, they often have free rein to access any data or application they need. However, in a zero-trust model, access is continuously verified, and users are only given access to the specific resources they need to perform their job.
Better compliance: A zero trust model can help organizations meet regulatory compliance requirements by providing granular access control and ensuring that all access requests are thoroughly authenticated and authorized.
Flexibility: With a zero trust model, organizations can move to a more cloud-based infrastructure, providing employees with more flexibility to work from any location, using any device. This approach can also reduce the complexity of traditional network security architecture.
Other reasons to adopt a zero trust strategy include:
- the increased movement of users, devices, applications, and data outside the enterprise perimeter,
- the growing risk exposure due to digital transformation,
- the ineffectiveness of the “trust but verify” approach against advanced threats and the complexity, and
- risk posed by traditional perimeters.
Read next: Only 15% of organizations have a mature level of cybersecurity readiness – Cisco study








