Cybersecurity trends in the first quarter of 2022 were more about evolution than revolution. Trellix Threat Report for Q1 2022 finds that attackers are using advanced technologies to carry out ransomware and malware attacks and breach email security. It has also been identified that attackers are exploiting vulnerabilities present in building access control systems, and healthcare.
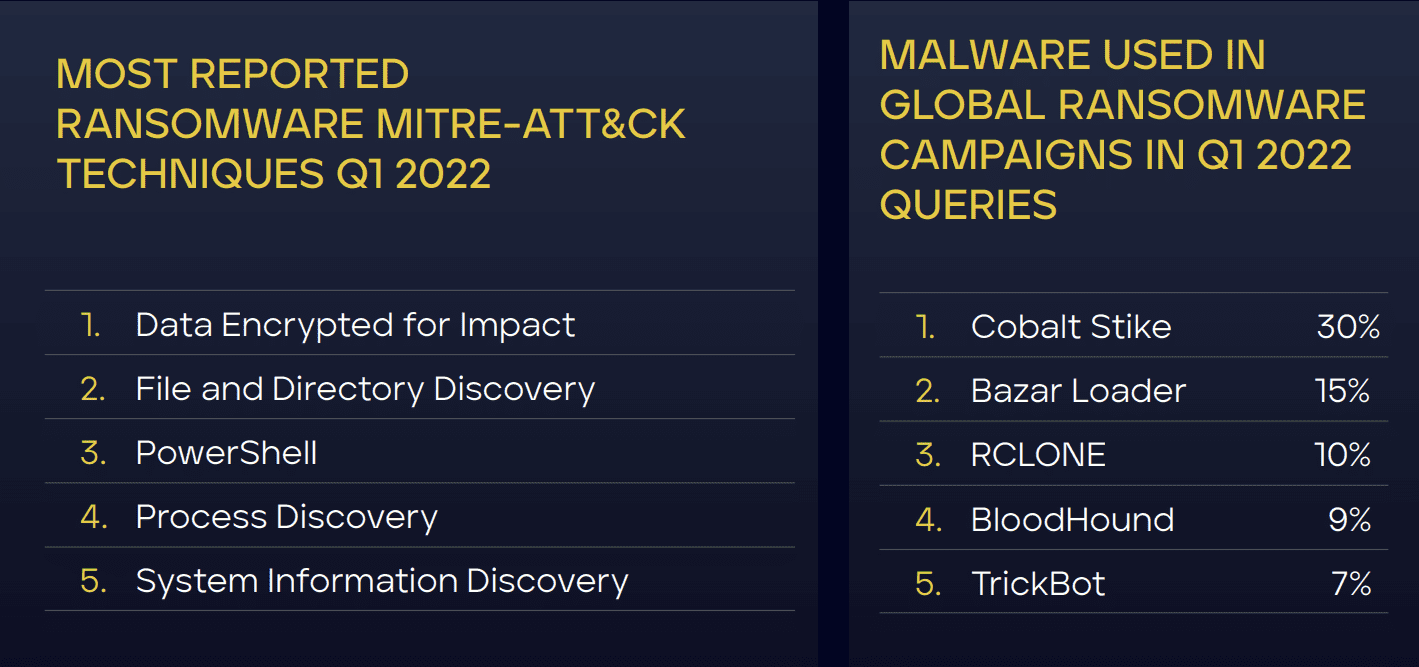
Ransomware and malware status in Q1 2022
In the global customer sector ransomware category, Telecom topped with 53% of detections among the top-10 sectors for the second consecutive quarter. Other customer sectors include business services, media & communications, finance, Transportation & Shipping. Ransomware Family detections were down in Q1 of 2022 with Lockbit accounting for 20% of top-10 ransomware tool queries, followed by Conti (17%), and Cuba (14%) in Q4 of 2021. However, queries of Lockbit, Conti, and Cuba decreased by 44%, 37%, and 55% respectively in Q1 of 2022 as compared to Q1 of 2022.
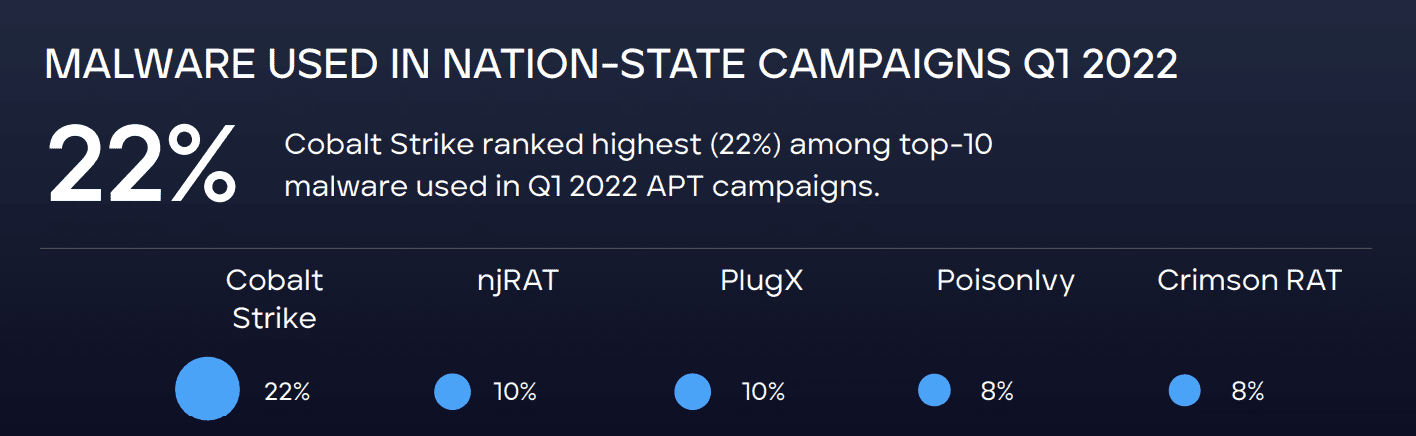
According to the Trellix report, Nation-State activity in Turkey accounted for 31% of the top 10 detections among client countries in Q1 2022, followed by Israel (18%), the United Kingdom (11%), Mexico (10%), and the United States (8%).
Critical flaws in building access control systems
“The average cost of a physical security compromise is 3.54 million dollars and takes an average of 223 days to identify a breach” – reveals an IBM study.
Critical infrastructure remains the most attractive target for criminals. The legacy systems in this industry contain hardware and software flaws, configuration issues, and update cycles that are also sluggish. Access control is one most overlooked area of industrial control systems. Access control systems provide automation and remote management for card readers and entry/exit points to secure locations.
Connected healthcare cybersecurity
The medical industry is at risk of cyberattacks because it has many devices that are not found in other industries. These devices include anesthesia machines, IV pumps, point of care systems, MRI machines, and others. Because these devices are not common, people do not think about security as much when it comes to the medical industry. Medical devices and software often have weak security practices, like not handling credentials well. They are also much prone to RCE (remote code execution) vulnerabilities. This makes connected healthcare an easy target for cybercriminals. Hence, timely steps must be taken to prevent such attacks.
Email security trends
Phishing URLs and malicious document trends in email security during Q1 2022. The majority of the malicious emails detected contained a phishing URL for stealing credentials or luring the victims to download malware. Next in popularity were emails with malicious documents attached in the form of Microsoft Office files or PDFs. These documents contain macros that work as downloaders or exploits helping the attacker gain control of the victim system. Another email security breach trend observed was several emails with malicious executables like info stealers or trojans attached.
The exploits used include malicious RTF files, MS Office documents with weaponized OLE objects, PDFs infected with Adobe Reader exploits, and malicious JS scripts. The following figure shows the top three file formats.

Image and source credits: Trellix Threat report
Read next: Perception Point launches Advanced Browser Security for eliminating web browser threats