As enterprises consistently shift towards technology as a service (XaaS), the production workloads are shifting to the public cloud platforms. With this, about 46% of the heterogenous mix of server workload types are expected to shift from VMs and bare metal to containers and serverless platforms in next one year.
Given the rapid increase in serverless platforms usage, companies must also know the related security threats, and the need to understand and implement the security measures to manage threats, says a new Enterprise Strategy Group (ESG) study that looks at the processes involved in and employed by the organizations to secure cloud-native applications.
Analysts at Data Theorem polled 371 IT and cyber security professionals in North America to create Security for DevOps – Enterprise Survey Report.
Survey highlights – the DevSecOps approach is emerging for securing cloud-native applications
The analysts have found that the DevSecOps is an emerging concept to handle the rising cloud security challenges.
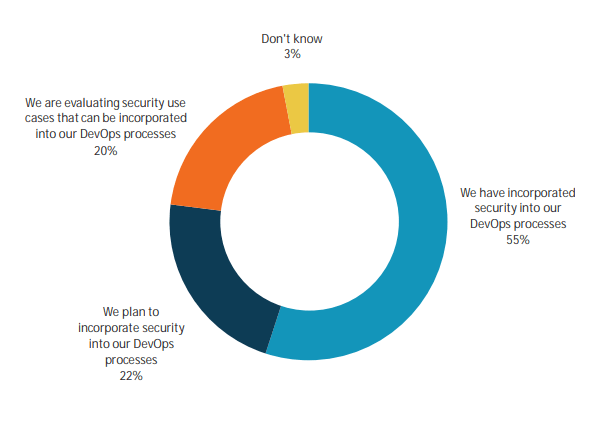
The study shows that 84 percent of the organizations have already incorporated security into their DevOps processes to some extent.
It also found that 8 percent companies are presently securing their cloud-native applications with DevSecOps (DevOps with Security) practices. This is again expected to rise. 68 percent of organizations said they are planning to secure 75% or more of their cloud-native applications with DevSecOps practices in two years.

About one in five companies has a unified approach to secure cloud-native applications. Overall, 82% of companies agreed to have different teams that are responsible for securing the cloud-native applications. Out of these, 52% have plans to merge these responsibilities in future.
However, when it comes to implementing security controls, only 22% of organizations aimed to embed security throughout the development process.
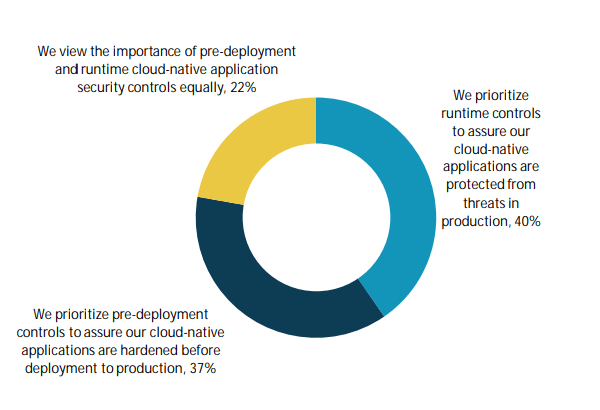
The study also found that out of all the cloud-native applications security controls, malware detection and prevention (32%) and vulnerability scanning (30%), both performed post deployment are the most commonly identified security controls.
While most of the organizations are aware about DevSecOps strategy and some have even started to implement in the process, many are still facing challenges to cover their applications.
What made security implementation difficult was the shortage of skilled security professionals, need for team collaboration, and lack of cloud security skills. Plus, the use of many technologies is complicating the process.
Given that, the CIOs, development and security teams have to work together to analyze and create threat models, integrate tools into the development process to protect cloud-native applications, and prioritize pre-deployment and runtime controls.
CIOs should now clearly understand that a deep collaboration across teams is significant in integrating security to the complete software delivery lifecycle.
READ NEXT: Cloud and service providers to drive growth in datacenter capacity: 451 Research









Nice Blog. Thanks for sharing your DevOps experience, Keep sharing more blog posts.